Archive
Cloning Virtual Machines using Hyper-V Without the Pain
This post will explain how to create and then clone virtual machines using Microsoft’s Hyper-V virtual machines. There are a few speed bumps you may encounter along the way that are helpful to know of in advance, and we’ll cover an approach to get over them.
I have been a long time user of VMWare for creating virtual machines, but, I ran into problems with hosting Microsoft’s ISA Server inside of a VMWare virtual machine. With the release of Windows Server 2008 and Hyper-V the story is different now. Microsoft supports ISA Server and their beta ISA Server product called TMG (Threat Management Gateway) in a virtual machine environment. See: http://technet.microsoft.com/en-us/library/cc891502.aspx and http://www.subodh.com/Blog/EntryId/47/Running-ISA-Server-2006-under-Hyper-V.aspx and finally Jim Harrison’s presentation on virtualizing ISA at http://edge.technet.com/Media/Virtualize-your-ISA-or-Forefront-TMG-servers/. Now it is possible to model an entire network along with ISA Server inside virtual machines. Additionally, the cloning of virtual machines, although a manual process, is sustainable.
That is the good news, however there are two gotcha’s:
- SID creation
- Mouse not captured in Remote Desktop Session
Let’s look at solving SID creation problems first, since that is the last thing I worked with and is freshest in my mind. If you are running stand alone machines, and are cloning from a parent virtual machine or vhd file, all of your vm’s will have the same SID. This is not a problem for you. If, however, you need to clone vm’s and then join a domain, you will have problems if you do not create a unique SID for each VM.
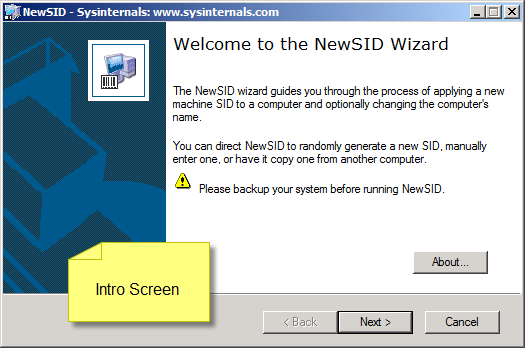
One way to do this is to use Microsoft’s sysprep tool, the other is to use a tool called NewSID located here http://technet.microsoft.com/en-us/sysinternals/bb897418.aspx, which the rest of this post will cover. There are some problems that the SYSPREP tool has as is reflected in this Microsoft Knowledgebase post: http://support.microsoft.com/kb/954356.
I choose NewSID because it only does two things; generates a new SID and renames the machine. And, that is all I need. If you have other requirements, SYSPREP is the way to go.
Ok, gotcha one. You will need to check for a specific registry entry in your seed virtual machine that will throw NewSID into an infinate loop which will cause it to run out of resources and crash. You need to see if you have the following registry key. If you don’t then you can go to the next step. The key to check for is HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Wow6432Node. The following blog post alerted me to the problem: http://forum.sysinternals.com/forum_posts.asp?TID=14370. After deleting the key in my seed vm, I had no further problems.
The second gotcha involves the creation of a VM using remote desktop; basically, you can’t do it, and in my mind is one of the most lame and frustrating things about Hyper-V. It is simple to create virtual machines using remote desktop with VMWare’s product and I don’t know how Microsoft could have let this out the door without remote desktop support, but they did.
So, you need to be physically in front of your host machine to install Microsoft’s Virtual Machine Integration Services to be able to use a mouse when working with virtual machines remotely. After you create your virtual machine and login, it’s a single mouse click to install these services, but you have to be physically at the console.
Now that the gotcha’s are out of the way here are the steps we will follow in creating a virtual machine in Hyper-V that is clonable.
- Create and configure seed vm.
- Copy the virtual hard disk or vhd file.
- Tweak child.
Before you can use Hyper-V you’ll need to create the Hyper-V role. And, before you create the role, it is important that you have enough physical NIC cards to support it. At least two are preferable. One for remote access, the other to use for the creation of virtual networks. When I created my Hyper-V role, I chose External for the network on my second NIC card which is used for by the virtual machines.
When you create your first vm, my advice is to select the defaults and let the Hyper-V manager put things where it wants to so you can learn where things go.
Before we continue – I am only explaining how to create vm’s with default values just to get you started. After creating your vm and working with it a bit, you’ll need to decide if the file structure is right for you along with naming conventions. I am just interested in providing a very basic orientation to this process to get you up in the air to circle the field a few times and then land.
The first thing to do is to create your virtual hard disk or the vhd file. This file is what will be cloned later. For now, create a new vhd with all defaults intact. To create the vhd file, click on the new link in the action pane on the right hand side at the top. After creating the vhd, then click new again to create a vm that will use the virtual hard disk you just created. Again, use the defaults until you get to connections. Choose the network you created when you created the Hyper-V role. The image below shows where the action menu is to complete these tasks.

After creating the vhd and vm, then click on it in the virtual machines pane in the top center. On the right you’ll see where you can change settings and start and connect. At this point you’ll want to install an OS on your new vm. Put your distrubution CD into the sever and click on start and follow the prompts to install your OS. There are other locations you can use for installing the OS such as a network install point.

After you get the OS installed, login to the machine and install the Virtual Machine Integration Service. To do that, click on the Action menu and select Insert Integration Services Setup Disk. It’s a virtual (what else!) CD that starts up automatically. Again follow the prompts and select defaults. You’ll need to restart the machine after tArehe install. At that point you can leave the console and the vm can be used via remote desktop.

This is the point where you tweak your vm until it is ready to distrubute. One of the items I strongly recommend you add is the NewSID program along with the registry change outlined earlier in the post. Also, one of the things I do with my seed vm is to never run it for general use, but only use it for creating clones and running them.
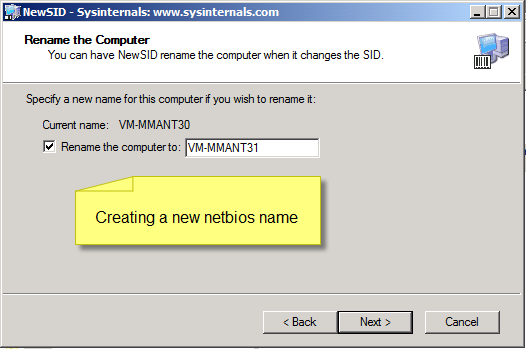
At this point we are ready to clone the vm. Go to the folder that houses your single vhd file and copy it and then give it a meaningful name. I usually give it the same name as the netbios name of the vm and the physical vm name, something like vm-mmant<n> where <n> is the last octet of the ip address in the subnet I use for my vm’s.

After the copy, create a new virtual machine and give it the same name you used for your vhd. Select the defaults until you get to the networking section and select your virtual network. In the next section, select the “Use an existing virtual hard disk.” It will give it the name of your machine and if your vhd is named the same you have one less step to take and everything ties together. Finish creating the vm and when you are done, click on start in its management section and wait a few seconds until it starts. Then click on connect and login. When the vm comes up, you can click on the Action menu and select the Ctrl-Alt-Delete option and then login.

The first thing to do is to change the IP address. Then fire up NewSID and select a new SID and then select a new netbios name for the vm and click ok. In a few minutes NewSID will finish and will reboot the box. When it comes back it will have its new SID, IP address and netbios name. The following images below display the steps in using NewSID to generate a new SID.


When the vm comes back and you login and are happy with the way everything is set up, I recommend that you create a snapshot before adding new roles and features. You can than go back to any snapshot if something gets messed up. Also, when you are done with the vm, you can go back to the original snapshot and use the vm for something else.
I hope that you found this post useful. If you have any questions or suggestions to make any of this more clear, please post and I’ll do my best to answer your questions.
Defect in Microsoft Sample Code Using Forms Authentication
If you are trying to use Forms Authentication and want to pass additional user data, there is a defect in the sample code provided by Microsoft.
The two errors are, (1) – when creating the FormsAuthenticationTicket, you must include the path of the cookie and (2) – you must create the authentication cookie using Response.Cookies.Add. the code provided below works:
protected void btnLogin_Click( object sender, EventArgs e )
{
bool isAuthenticated = IsAuthenticated( txtUserName.Text, txtPassword.Text );
if ( isAuthenticated )
{
string roles = GetRoles( txtUserName.Text );
FormsAuthenticationTicket CLAC = new FormsAuthenticationTicket( 1, txtUserName.Text, DateTime.Now, DateTime.Now.AddMinutes( 60 ), true, roles, FormsAuthentication.FormsCookiePath );
string encryptedTicket = FormsAuthentication.Encrypt( CLAC );
Response.Cookies.Add( new HttpCookie( FormsAuthentication.FormsCookieName, encryptedTicket ) );
Response.Redirect(FormsAuthentication.GetRedirectUrl( txtUserName.Text, false ));
}
}
I tried changing the code, and instead of calling Response.Redirect using the FormsAuthentication.FormsCookieName method using FormsAuthentication.RedirectFromLoginPage(). This did log the user on, but the user data never showed up. The problem in using the Microsoft example code was that the the auth cookie never got written. Using the Response.Cookies.Add() method to create the cookie, and including the path when creating the auth ticket is what solved that problem.
The blog post that helped me out was http://authors.aspalliance.com/aspxtreme/sys/web/security/FormsAuthenticationTicketClass.aspx.
Exchange UCE Default Filter Level Changes
In checking my Exchange Server 2007 logs tonight, I noticed a message in the event log that concerned me.
My concern is that I have not touched the UCE filter since I set up the server and I do not know what is triggering these changes. In searching around the internet, I found the following post that indicated this is a bug in Exchange server. Here is the relevent portion of the article:
Changes to the gateway threshold inadvertently report that the store threshold was modified
When a change is made to the gateway threshold, the Exchange store reports that the store threshold has been modified in the event log even if it has not been modified. Following is a description of the event:
The Unsolicited Commercial Email default filter level has been updated. The new value is n.
This event is recorded because the user interface (UI) rewrites both values in Active Directory regardless of whether the store threshold value has changed. The Exchange store is notified of the change and writes the event entry.
The full link is here: http://support.microsoft.com/kb/867633
Microsoft’s Entity Framework
I have been wrestling with programming patterns that bring data to the UI, and I am looking at three ways to do it:
- the hand rolled datalayer
- LINQ
- Entity framework
In this series of posts, I’ll share lessons learned and bits and pieces of how to make things work, like the best way to use stored procedures in LINQ and so forth.
I also have a really great book to recommend. It’s “Programming Entity Framework” by Julia Lerman. This is a really great book. She takes you through a very complex and feature rich subject. The only nit I have to pick with this book is that many of the examples are wrong. If you follow instructions, your stuff will break. This is very unfortunate because at the earliest stages of the learning process, one never knows why something truly went wrong, or if you are learning something the wrong way.
I wish publishing companies would just print a few copies of the book and either give it to people or simply pay them to walk through all of the exersizes in the book and catch what is wrong.
Basically, it’s a nit and well worth the price of admission to this subject.
How we move data around is really important, and frameworks and design patterns help us. The Entity Framework is a very important framework and design pattern to learn. Microsoft has put a lot of money into it, and this framework has won the internal battle. The LINQ team has been merged into the Entity Framework team and LINQ is basically going to tread water and quietly go away.
There is a lot to be said for the ability to look at a programming problem from a domain perspective. I can’t tell you the number of times I have had to redirect high level design sessions away from the physical database into requirements and business rules. One of the benefits of the Entity Framework is the way it influences design conversations.
Dr. Peter Chen has written extensively about the structure of design elements feeding back into language and vice versa. Here are links to a few of his papers:
- The entity-relationship model: Toward a unified view of data
- Entity-Relationship Modeling: Historical Events, Future Trends, and lessons Learned
- From Ancient Egyptian Language to Future Conceptual Modeling
- English Sentenence Structure and Entity-Relationship Diagrams
- The entity-relationship model – A basis for the enterprise view of data
- English, Chinese and ER Diagrams
- A Preliminary Framework for Entity-Relationship Models

Recent Comments